A common operational requirement for an SOA is the ability to determine if a service is available. Just as it is common to ping a machine, we also want to be able to ping an individual service to determine that it is running and able to respond to messages.
Our first pass at solving this issue was to introduce an IPingable interface that each of our service facades would implement. The code was pushed into our service base class and the software factory updated as appropriate. However, this didn’t feel quite right. Other service extensions such as the metadata endpoint were not so invasive, it can be established by a simple addition to the service configuration file. We felt we wanted the same configurable nature for a ping mechanism and so set out to figure out how to create a custom WCF behavior.
This post walks through the creation of a WCF Endpoint Behavior which will add a Ping() method to a service. The method returns the DateTime, in UTC, stating when the server processed the request. This can be used to establish how long a basic roundtrip to the service is taking for both the request and the reply. The use of an endpoint behavior allows us to add this functionality to any service, therefore we can add it retrospectively to services that we have already created without needing to change them.
The source code for this post is available from my DropBox.
Let’s start by looking at how we would configure such an endpoint behavior. For an existing service, we would copy the assembly containing the endpoint behavior into the bin folder for the service and then add some entries into the web.config:
<configuration>
<system.serviceModel>
<extensions>
<behaviorExtensions>
<add name="Ping" type="CustomWcfBehaviors.PingEndpointBehavior, CustomWcfBehaviors" />
</behaviorExtensions>
</extensions>
<behaviors>
<endpointBehaviors>
<behavior>
<Ping>
</behavior>
</endpointBehaviors>
</behaviors>
We register the type [CustomWcfBehaviors.PingEndpointBehavior in assembly CustomWcfBehaviors] that is our custom behavior as a behavior extension and then declare that we want to use the extension. The configuration above sets up a default behavior that will be applied to all endpoints since we haven’t explicitly named it. That’s it, fetch the metadata for the service it will now contain a Ping() method.
The configuration of the behavior is reasonably straight forward, let’s look at the implementation…
namespace CustomWcfBehaviors {
public class PingEndpointBehavior: BehaviorExtensionElement, IEndpointBehavior {
private const string PingOperationName = "Ping";
private const string PingResponse = "PingResponse";
The behavior needs to derive from BehaviorExtensionElement which allows it to be declared in the service configuration as an extension element. We need to introduce two overrides:
// factory method to construct an instance of the behavior
protected override object CreateBehavior(){
return new PingEndpointBehavior();
}
// property used to determine the type of the behavior
public override Type BehaviorType{
get { return typeof(PingEndpointBehavior); }
}
Now onto the real work, the IEndpointBehavior implementation:
public void Validate(ServiceEndpoint endpoint) {}
public void AddBindingParameters(ServiceEndpoint endpoint, BindingParameterCollection bindingParameters) {}
public void ApplyClientBehavior(ServiceEndpoint endpoint, ClientRuntime clientRuntime) {}
public void ApplyDispatchBehavior(ServiceEndpoint endpoint, EndpointDispatcher endpointDispatcher) {
if(PingOperationNotDeclaredInContract(endpoint.Contract)) {
AddPingToContractDescription(endpoint.Contract);
}
UpdateContractFilter(endpointDispatcher, endpoint.Contract);
AddPingToDispatcher(endpointDispatcher, endpoint.Contract);
}
There are four methods that we need to implement but only one that we do any work in. The ApplyDispatchBehavior is where we add our code to manipulate how the endpoint invokes the service operations.
Endpoints map to the ABC of WCF [address, binding and contract]. What we want to do is extend the contract with a new service operation. A service host may allow multiple endpoints to expose the service contract on different protocols. For example, we may choose to host our service using both http and net.tcp. If we use IIS as our service host, this is configured via the Advanced Settings… of the Manage Application… context menu option.
The ‘Enabled Protocols’ lists the protocols we want to use. If we have more than one protocol listed then we have to take care that we don’t attempt to add the new Ping operation multiple times to our contract – once per binding type. To check that we haven’t already added the operation we call a small Linq query…
private bool PingOperationNotDeclaredInContract(ContractDescription contract) {
return ! contract
.Operations
.Where(operationDescription =>
OperationDescription.Name.Equals(PingOperationName,
StringComparison.InvariantCultureIgnoreCase))
.Any();
}
If the Ping operation is not found then we need to add it:
private void AddPingToContractDescription(ContractDescription contractDescription) {
OperationDescription pingOperationDescription = new
OperationDescription(PingOperationName, contractDescription);
MessageDescription inputMessageDescription = new MessageDescription(
GetAction(contractDescription, PingOperationName), MessageDirection.Input);
MessageDescription outputMessageDescription = new MessageDescription(
GetAction(contractDescription, PingResponse), MessageDirection.Output);
MessagePartDescription returnValue = new MessagePartDescription("PingResult",
contractDescription.Namespace);
returnValue.Type = typeof(DateTime);
outputMessageDescription.Body.ReturnValue = returnValue;
inputMessageDescription.Body.WrapperName = PingOperationName;
inputMessageDescription.Body.WrapperNamespace = contractDescription.Namespace;
outputMessageDescription.Body.WrapperName = PingResponse;
outputMessageDescription.Body.WrapperNamespace = contractDescription.Namespace;
pingOperationDescription.Messages.Add(inputMessageDescription);
pingOperationDescription.Messages.Add(outputMessageDescription);
pingOperationDescription.Behaviors.Add(new DataContractSerializerOperationBehavior(pingOperationDescription));
pingOperationDescription.Behaviors.Add(new PingOperationBehavior());
contractDescription.Operations.Add(pingOperationDescription);
}
Here we are creating an OperationDescription to add to our ContractDescription, this adds the operation specification for our Ping operation to the existing contract. The code to execute is encapsulated by the PingOperationBehavior().
public class PingOperationBehavior : IOperationBehavior {
public void ApplyDispatchBehavior(OperationDescription operationDescription, DispatchOperation dispatchOperation) {
dispatchOperation.Invoker = new PingInvoker();
}
public void Validate(OperationDescription operationDescription) {}
public void AddBindingParameters(OperationDescription operationDescription, BindingParameterCollection bindingParameters) {}
public void ApplyClientBehavior(OperationDescription operationDescription, ClientOperation clientOperation) {}
}
Similar to the endpoint behavior, we need to implement an interface in this case the IOperationBehavior. The method signatures are similar and we need to fill out the ApplyDispatchBehavior method to call an IOperationInvoker to execute our Ping implementation:
internal class PingInvoker : IOperationInvoker {
public object[] AllocateInputs() {
return new object[0];
}
public object Invoke(object instance, object[] inputs, out object[] outputs) {
outputs = new object[0];
return DateTime.UtcNow;
}
public IAsyncResult InvokeBegin(object instance, object[] inputs, AsyncCallback callback, object state) {
throw new NotImplementedException();
}
public object InvokeEnd(object instance, out object[] outputs, IAsyncResult result) {
throw new NotImplementedException();
}
public bool IsSynchronous {
get { return true; }
}
}
The ping operation is so simple that there is no asynchronous implementation. All we do is return the current date time on the server in UTC.
So where are we? Well, we’ve added the Ping method to our existing service contract and mapped it to an IOperationBehavior which will dispatch an IOperationInvoker to call the code.
Next up, we have to update the endpoint dispatcher so that it knows what to do if it receives a Ping request message. The endpoint dispatcher maintains a list of actions that it knows how to action. We need to update this list so that it includes our new ping action. To do this we just refresh the action list from the contract description operations:
private void UpdateContractFilter(EndpointDispatcher endpointDispatcher, ContractDescription contractDescription) {
string[] actions = (from operationDescription in contractDescription.Operations
select GetAction(contractDescription, operationDescription.Name)
).ToArray();
endpointDispatcher.ContractFilter = new ActionMessageFilter(actions);
}
Finally we need to add a new dispatch operation to the endpoint dispatcher so that it calls our PingOperation when the Ping action is received.
private void AddPingToDispatcher(EndpointDispatcher endpointDispatcher, ContractDescription contractDescription) {
DispatchOperation pingDispatchOperation = new DispatchOperation(endpointDispatcher.DispatchRuntime,
PingOperationName,
GetAction(contractDescription, PingOperationName),
GetAction(contractDescription, PingResponse));
pingDispatchOperation.Invoker = new PingInvoker();
endpointDispatcher.DispatchRuntime.Operations.Add(pingDispatchOperation);
}
private string GetAction(ContractDescription contractDescription, string name) {
string @namespace = contractDescription.Namespace;
if(!@namespace.EndsWith("/")) { @namespace = @namespace + "/"; }
string action = string.Format("{0}{1}/{2}", @namespace, contractDescription.Name, name);
return action;
}
Well, we are now done on the server side. We’ve created a couple of new classes:
• PingEndpointBehavior
• PingOperationBehavior
• PingInvoker
These three classes allow us to add a Ping method to a service by adding the Ping behavior via the service configuration file.
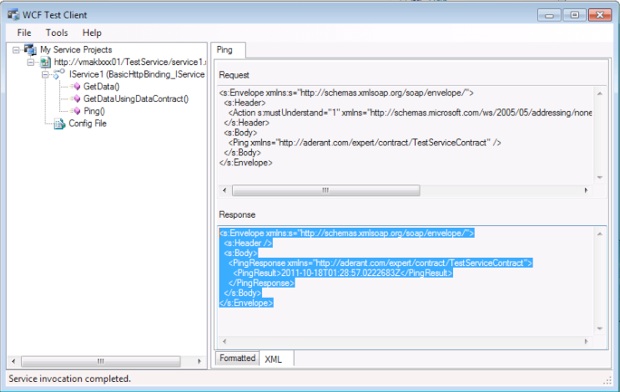
To test this, you can use the WcfTestClient application. The sample code demonstrates this by calling Ping on a standard WCF and WF service created by Visual Studio, see my DropBox.
In the next post I’ll discuss how we create a generic service proxy to call Ping.
UPDATE: the code works for the basicHttpBinding but not for wsHttpBinding.
UPDATE: Code now available from github.com/stefsewell/WCFPing